ICCID (Integrated Circuit Card Identifier) is a unique 19-digit number that is assigned to every SIM card in the telecom industry. It serves as an important identifier for tracking and managing subscriber accounts, and is used to authorize access to various telecom services. With the increasing number of mobile subscribers, ICCID database management has become critical to ensure the accuracy and security of subscriber data.
Data accuracy and security are key components of ICCID database management. Inaccurate data can lead to billing errors, incorrect subscriber information, and poor customer experience. Additionally, security breaches can lead to data theft, unauthorized access, and loss of customer trust. In this article, Cmd99 will explore the importance of data accuracy and security in ICCID database management, and discuss strategies for ensuring both.
Importance of Data Accuracy and Security in ICCID Database Management
Data accuracy and security are crucial in ICCID database management because they directly impact customer satisfaction and business operations. Inaccurate data can lead to billing errors and incorrect subscriber information, which can cause delays in resolving customer issues and lead to dissatisfaction. Furthermore, inaccurate data can result in erroneous billing and financial losses for the telecom operator.
Data security is equally important in ICCID database management because subscriber information is sensitive and confidential. Unauthorized access or data breaches can lead to loss of customer trust, regulatory violations, and potential legal action. In addition, data breaches can result in financial losses due to loss of reputation and legal costs.

Strategies for Ensuring Data Accuracy in ICCID Database Management
Ensuring data accuracy in ICCID database management is crucial to maintaining customer satisfaction and reducing financial losses. Here are some strategies for ensuring data accuracy:
- Regular Data Audits and Validation: Regular data audits and validation can help identify and correct inaccurate data. These audits can be performed manually or using automated tools that check for consistency and completeness of data.
- Implementing Quality Control Measures: Quality control measures can be put in place to ensure that data is entered correctly in the first place. For example, mandatory fields can be implemented in the user interface to ensure that all required data is entered.
- Maintaining Up-to-Date Records: Keeping records up-to-date is crucial to ensuring data accuracy. This can be achieved by periodically reviewing subscriber data and updating records as necessary.
Strategies for Ensuring Security in ICCID Database Management
Ensuring data security in ICCID database management is equally important to protecting sensitive subscriber information and maintaining customer trust. Here are some strategies for ensuring data security:
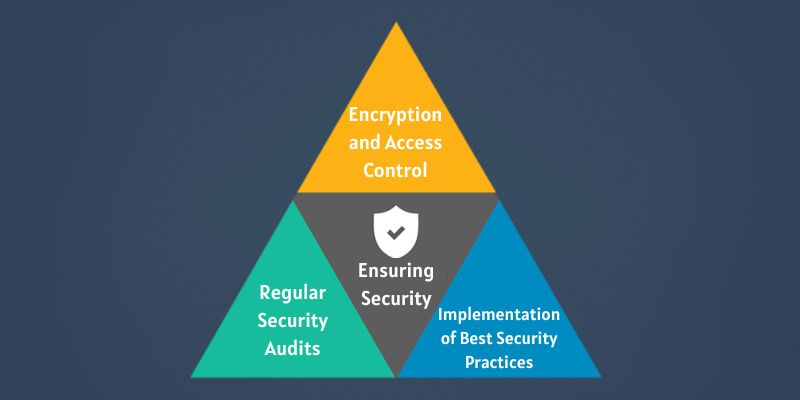
- Encryption and Access Control: Encryption can be used to protect sensitive subscriber data from unauthorized access. Access control measures, such as role-based access control, can be implemented to restrict access to sensitive data only to authorized personnel.
- Regular Security Audits: Regular security audits can help identify potential security vulnerabilities in the ICCID database. This can be achieved by performing vulnerability assessments and penetration testing to identify potential threats.
- Implementation of Best Security Practices: Implementation of best security practices, such as regularly changing passwords, can help prevent unauthorized access to the ICCID database.
Role of Technology in ICCID Database Management
Technology plays an important role in ICCID database management. Automated data processing and validation tools can help ensure data accuracy and consistency, while advanced security features can help protect sensitive subscriber data. Integration with other telecom systems can also improve the accuracy and efficiency of ICCID database management.

Automated Data Processing and Validation: Automated data processing and validation tools can help reduce errors in ICCID database management by automatically validating data and checking for consistency and completeness. This can help reduce the time and effort required for manual data processing and improve data accuracy.
Advanced Security Features: Advanced security features, such as encryption and access control, can help protect sensitive subscriber data from unauthorized access. Encryption can be used to secure data at rest and in transit, while access control measures can restrict access to sensitive data only to authorized personnel. Regular security audits and vulnerability assessments can help identify potential security vulnerabilities in the ICCID database and ensure that appropriate security measures are in place.
Integration with Other Telecom Systems: Integration with other telecom systems can improve the accuracy and efficiency of ICCID database management. For example, integration with the billing system can help ensure that billing information is accurate and up-to-date, while integration with the customer relationship management (CRM) system can improve customer service by providing accurate and timely subscriber information.
Conclusion
In conclusion, ICCID database management is a critical aspect of the telecom industry that plays a significant role in ensuring the accuracy and security of subscriber data. Data accuracy and security are vital components of ICCID database management, as they can directly affect customer satisfaction and business operations. Therefore, strategies such as regular data audits, quality control measures, up-to-date record keeping, encryption and access control, and regular security audits should be implemented to ensure data accuracy and security.
Moreover, technology plays a crucial role in ICCID database management, with automated data processing and validation tools, advanced security features, and integration with other telecom systems helping to improve the accuracy and efficiency of the process. By implementing these best practices and leveraging technology, telecom operators can ensure the highest levels of customer satisfaction and operational efficiency, while protecting sensitive subscriber data from unauthorized access and theft.